TL;DR
- Define who can perform which actions.
- Protect data security and user privacy.
- Managed through roles and access levels.
- Applied across apps, teams, and systems.
Definition
Permissions are rules within a system that regulate access to features, functions, or data, ensuring that users and processes operate within defined boundaries.
Detailed Overview
Permissions are a cornerstone of digital security and organizational control. They govern who can view, edit, delete, or share information, as well as who can perform sensitive actions such as changing settings or managing users. By enforcing permissions, systems maintain both safety and order, preventing unauthorized use while supporting collaboration.
A frequent question is how permissions differ from roles. Permissions are granular rules, while roles are collections of permissions grouped for convenience. For example, an “editor” role in a content management system may include permissions to add and edit articles but not to publish or delete them. Roles simplify administration by bundling permissions into logical sets.
Another common query relates to why permissions are so critical. Without clear boundaries, sensitive information can be exposed or modified incorrectly. For businesses, poor permission structures often lead to data leaks, compliance violations, or accidental changes that disrupt workflows.
Teams also ask about permissions in collaborative environments. In design or product tools, permissions define whether someone can comment, edit, or only view. This structure protects work while enabling meaningful collaboration. For example, a stakeholder might have comment-only access to provide feedback without disrupting design files.
Accessibility is also part of the discussion. Permissions need to balance security with usability. Systems that are overly restrictive frustrate users, while those that are too permissive compromise safety. The best systems provide flexibility, allowing administrators to tailor permissions to specific contexts while keeping defaults clear and simple.
Finally, permissions must evolve as organizations grow. What works for a small team may not scale to an enterprise with multiple departments. Modern systems often include advanced permission management, such as group-level controls, conditional access, and integration with identity providers.
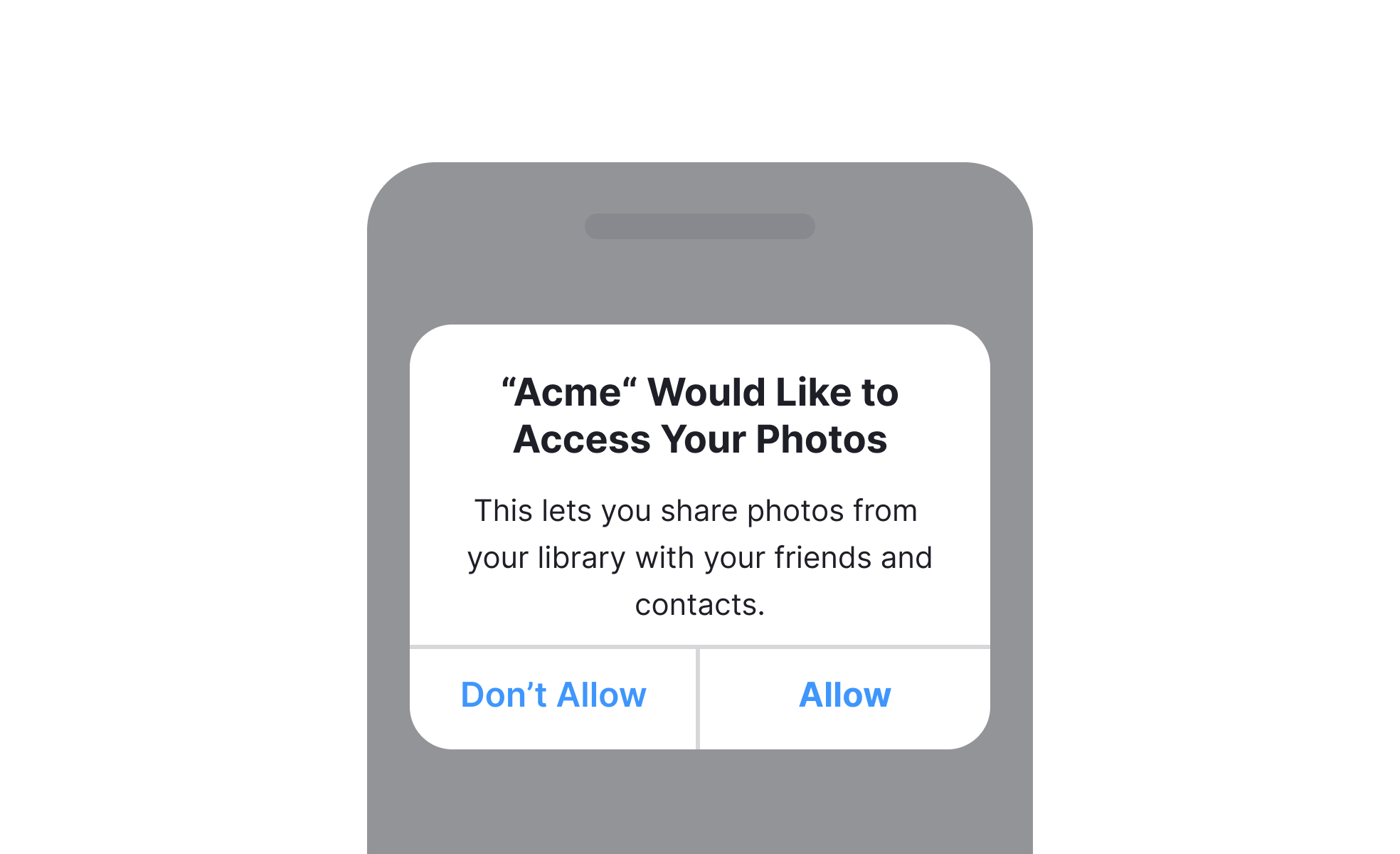
Learn more about this in the Give Users a Reason to Grant Permissions Exercise, taken from the Requesting User Permission Lesson, a part of the Common Design Patterns Course.
















